Table of Contents
Are You Worried About Computer Security And Privacy? If not, then start thinking now! Now the computer has become a personal thing more than our Manibag. Here we store all the private and working data, do the banking, the necessary accounts are logged-it is far from being a computer hack, we do not want any relatives to physically access this machine.
It is possible to prevent anyone from using a physical password using a password, but if you use a family computer, your computer needs to be shared even if you do not want it. Besides, if there are a small brother and sister in the house then it is necessary to tell the password. So, in the absence of your computer, it is necessary to know when you are using it.
The Camera Never Lies
If you have a webcam installed on your computer or if you use a laptop, then there is definitely a webcam install. Now, naturally, the camera is possible to take pictures of any person sitting in front of the computer. But how will you make this webcam your slavery, how do you make it sting? It is very easy to download appear software from here.
Only after installing, you can understand how much work it really is. This software has many powerful features, and maybe you have been looking for something like this for so long. The software offers a lot of benefits including video record, audio record, access to your recorded files online. The software is easy to use, open with tabs on its various options.
You can interrupt all the settings and make it yourself. Moreover, this software supports the Malti Video Stream. Again you can set video bitrate and resuscitation as desired. Motion detection is a deadly feature of the software. Since you have set up your webcam, to monitor whether someone is sitting on your computer. so the camera record is always on the screen, only if someone is in front of the computer. This feature works exactly like this.
You can set sensitivity from your camera settings, if the camera sees moving objects according to the sensibilities, the camera will start recording it. Moreover, this software has the ability to automatically upload recorded videos to YouTube. But before starting this feature, think a little bit, you do not want to have a video of the house that should not have been done! (I mean, what do you mean?). However, the feature will be very powerful, more than just accessing the video online can be nothing. Before turning on the upload option on YouTube, check that your firewall does not block the uploading.
Actually, the software has many fun things to do, but to make sure all of them, this whole article will be for this software only. You install and explore features by yourself.
Check Logs And Recency Files
Today’s children are very distant, the kids have become very clever. Everyone knows that what is being done on Windows computers is stored in logs and recent, so if someone steals your computer before using it, then clear the log and restore a file. But still knowing logs and recency files is a smart thing to do.
To check the Windows computer logs, go to the Computer Management Tool, from there the event viewer and its under Windows logs. And from here you will definitely see all the computer’s accessed information. When you were logged in to a computer, what keyword search was done in the file explorer when the user logged off, etc. Although most of the time, these logs are about to delete, if your forehead is really good, you can get all the information.
It is easier to see the correct file, and even easier it is to delete them. From the time of Windows XP, people have to delete the Recent Access file logs to fasten the computer (even if they delete, nothing happens, so the computer does not fire). If you use Windows 10, right-click on any software icon from the Start menu or Task Bar, you will see a menu with an open list, where the software can see to have a file openly opened.
Keylogger
In fact, everything is using by yourself, you use bad things, or you can use it well. Like a bomb that helps people to build the railway lines again by breaking the mountains, it is possible to monitor your computer using keyloggers, though it is a hack tool. Keylogger is a software (malware) that is pressing a key on your computer keyboard, saving all the data. The webcam software that I have discussed at the beginning of this tune, is a child with this mind The Manhattan ends when Kenna covers the webcam with clothes. But the keylogger creat specifically to hide. Keylogger creates hidden processes and captures keyboard data.
Since all keyloggers are tarnished as malware, the antivirus program may a problem. So it is necessary to disable the antivirus when installing it. There are many free keyloggers that you can use. However, I will recapture the e-light keylogger.
Automatic Screenshot
If you do not want to use the keylogger for antivirus problems, then this option may be good for you. Time snapper is a tool that takes pictures of your computer screen after a few seconds. The use of this program is totally watery. It will start automatically after you install it. But this software can see in the system tray, so if someone sees the system tray, the software can be captured.
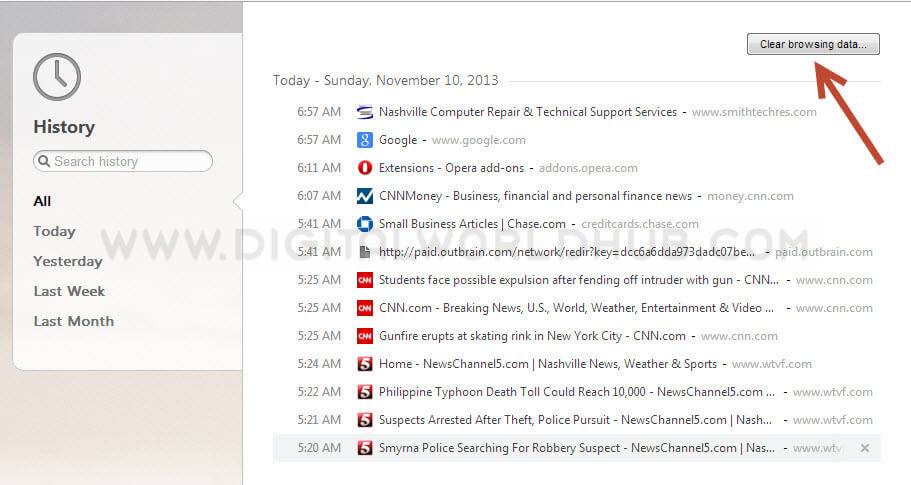
Browser History
If a public like me can steal your computer and open it. Then start the Web browser first by opening the browser. So it is a good idea to take a look at browsing histories. If luck is better then you can get information from browsing history. But there is more chance of getting it.